Top 5 Most Common Network Vulnerabilities: weak password policies
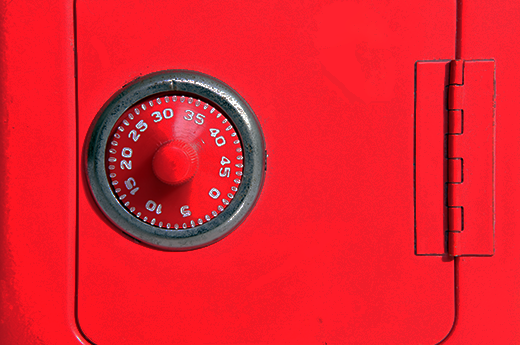
Part 1:5 Weak password policies – improve your network’s security
Here at Perspective Risk, we run frequent network penetration tests for clients of all sizes and security capabilities. We observe certain issues cropping up time and time again, which can significantly affect a business’ security posture.
During this series we will cover the top 5 issues we most commonly find, together with some simple remediation advice you can follow that should make a difference.
This 1st part focusses on weak password policies, why they shouldn’t be overlooked, and what you can do to improve the quality of your passwords.
Want to know more? Get in touch with one of our experts today
Password lockout thresholds – are they good enough?
Frequently, companies invest heavily in their external defence capability but fail to adequately protect the internal corporate domain. A common issue is the weakness of password policies, especially when it comes to privileged accounts, such as local or domain administrator users.
Often, a low lockout threshold – such as 3-5 attempts to lock an account, is used as an argument against more robust password policies. After all, if an attacker would lock an account so easily, how would password guessing attacks ever succeed?
It’s worth noting that internal networks are often vulnerable to several types of spoofing attacks, which trick users into connecting to the attacker’s machine, exposing hashed credentials. The hashes can then be attacked offline and at much greater speeds, such as millions of attempts per second on a system equipped with a single graphics card (and much more on dedicated cracking rigs). This bypasses the lockout threshold entirely, and any weak passwords will be soon recovered.
Password length, complexity and beyond
Following established advice on password length and complexity is a good first step. However, this does not mitigate users’ tendencies to pick passwords based on common words, with additional character substitutions.
For example, a user may choose a password such as Password1!, which may satisfy length and complexity requirements (at least 10 characters long and a mixture of upper- and lower-case letters, digits and special characters). Unfortunately, this is a commonly used password, and can be found in most dictionaries compiled for password cracking.
It may be more helpful to encourage users to use “pass phrases” with two or more words, which will greatly increase the search space required to succeed in a brute force attack. These may also be easier to remember than complex substitutions on a single word.
To illustrate this effect, the two examples below have been created using GRC’s Password Haystack tool. The first example is a shorter password with complex substitutions. The other is a three word passphrase using only lowercase letters:
The passphrase has an exponentially larger search space, even when using lowercase characters only. That being said, some common phrases may already be included in dictionaries used by attackers, and it’s recommended to add some randomness when choosing words.
Conclusions and password security help
This concludes the first article in our series of 5 common issues spotted on network penetration tests. When it comes to password security, here are some suggestions to consider:
- Don’t rely solely on lockout thresholds to protect against users’ choice of weak passwords; hashed credentials can be leaked from databases and the internal corporate network.
- There’s more to password strength than using difficult to remember character substitutions and complex characters – encourage users to use longer combinations of words which may be simpler to remember.
- Consider auditing your passwords periodically to identify accounts with weak passwords, especially privileged or administrative ones.
If you need help with any aspect or your information security, please call us on 0113 880 0722 or click here to contact us. Our expert team will be happy to advise you.
Want to check how good your organisation’s security is? Click here.

